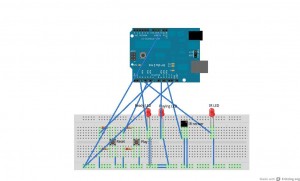
Here is a better view of how its put together:
And here is my uber 1337 code :P
#include < IRremote.h >
int IRRECV = 11;
int READYLED = 9;
int PLAYBUTTON = 5;
int IRLED = 3;
int RESETBUTTON = 7;
int PLAYLED = 2;
decode_results results;
IRrecv irrecv(IRRECV);
IRsend irsend;
void setup()
{
Serial.begin(9600);
irrecv.enableIRIn();
pinMode(READYLED, OUTPUT);
pinMode(PLAYBUTTON, INPUT);
pinMode(RESETBUTTON, INPUT);
pinMode(PLAYLED, OUTPUT);
}
int codeType = -1;
unsigned int rawCodes[RAWBUF];
int codeLen;
void rec(decode_results *results)
{
int count = results->rawlen;
codeLen = results->rawlen - 1;
for (int i = 1; i <= codeLen; i++) {
if (i % 2) {
rawCodes[i - 1] = results->rawbuf[i]*USECPERTICK - MARK_EXCESS;
Serial.print(" m");
}
else {
rawCodes[i - 1] = results->rawbuf[i]*USECPERTICK + MARK_EXCESS;
Serial.print(" s");
}
Serial.print(rawCodes[i - 1], DEC);
}
Serial.println("");
digitalWrite(READYLED, HIGH);
}
void play()
{
digitalWrite(PLAYLED, HIGH);
Serial.println(rawCodes[0]);
irsend.sendRaw(rawCodes, codeLen, 38);
delay(800);
digitalWrite(PLAYLED, LOW);
}
void reset()
{
int codeType = -1;
unsigned int rawCodes[RAWBUF];
int codeLen;
digitalWrite(READYLED, LOW);
setup();
}
void loop()
{
if (irrecv.decode(&results) && digitalRead(READYLED) == LOW) {
rec(&results);
irrecv.resume();
}
if (digitalRead(PLAYBUTTON) == LOW && digitalRead(READYLED) == HIGH)
{
play();
}
if (digitalRead(RESETBUTTON) == LOW)
{
reset();
}
}
Ok thats all i got, peace.

